Get Early Warning
Protect your business instantly with industry-leading 24/7 cyber protection – and no long commitments. Catch security breaches, malware, and vulnerabilities in your network that criminals can exploit. This sample report shows you what an Arctic EWS report looks like for the average company - so you can subscribe with confidence.
Arctic EWS is Arctic Security’s complete external monitoring service. It puts world-class cybersecurity between your network and cybercriminals for a price that’s actually affordable. And you can always try Arctic EWS for a month to see that it works for you, and easily cancel if it doesn't. If you find yourself enjoying Arctic EWS and want to keep at it, you’ll keep on benefitting from a service that:
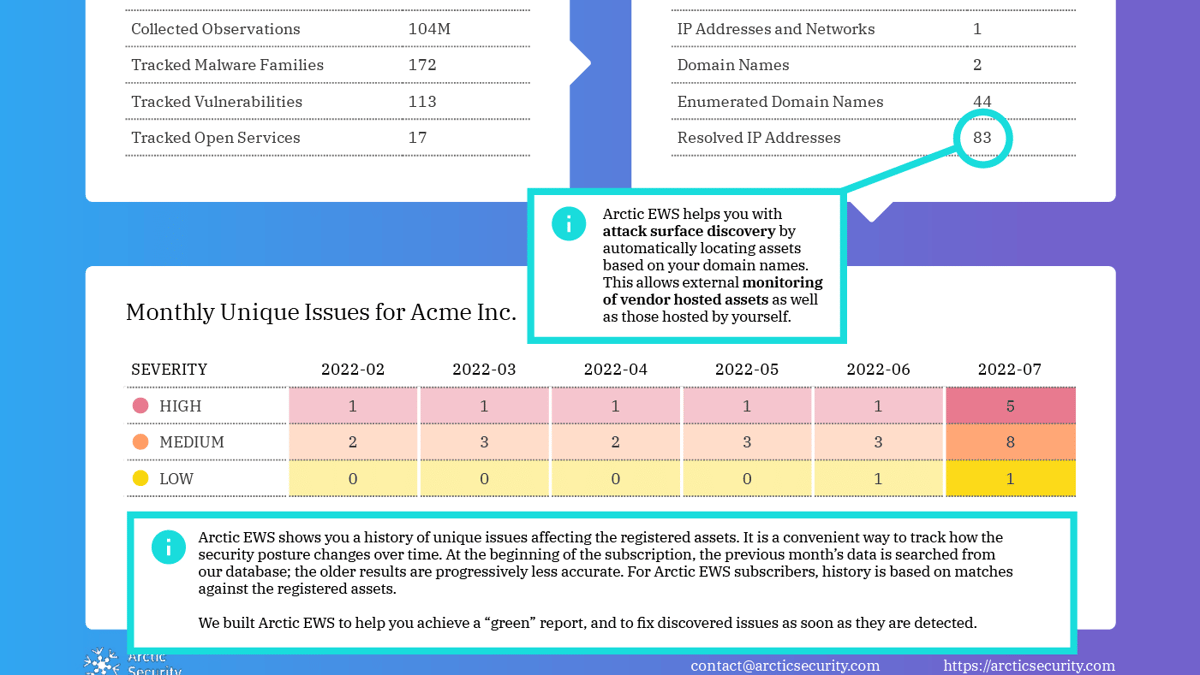
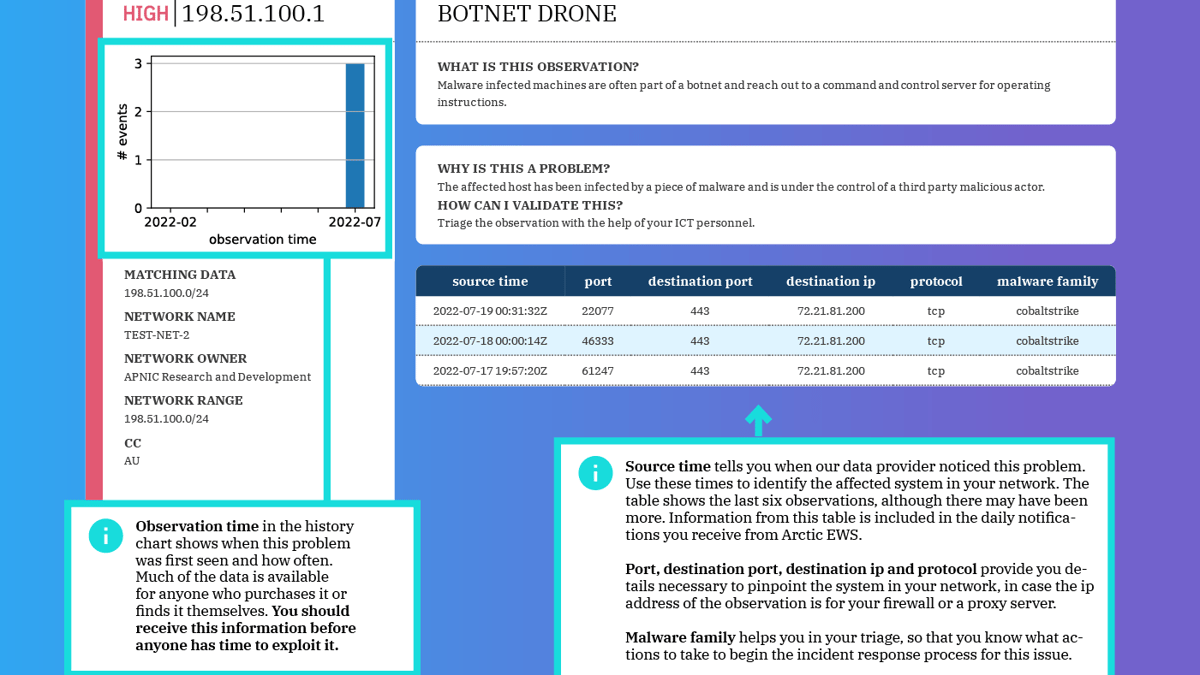
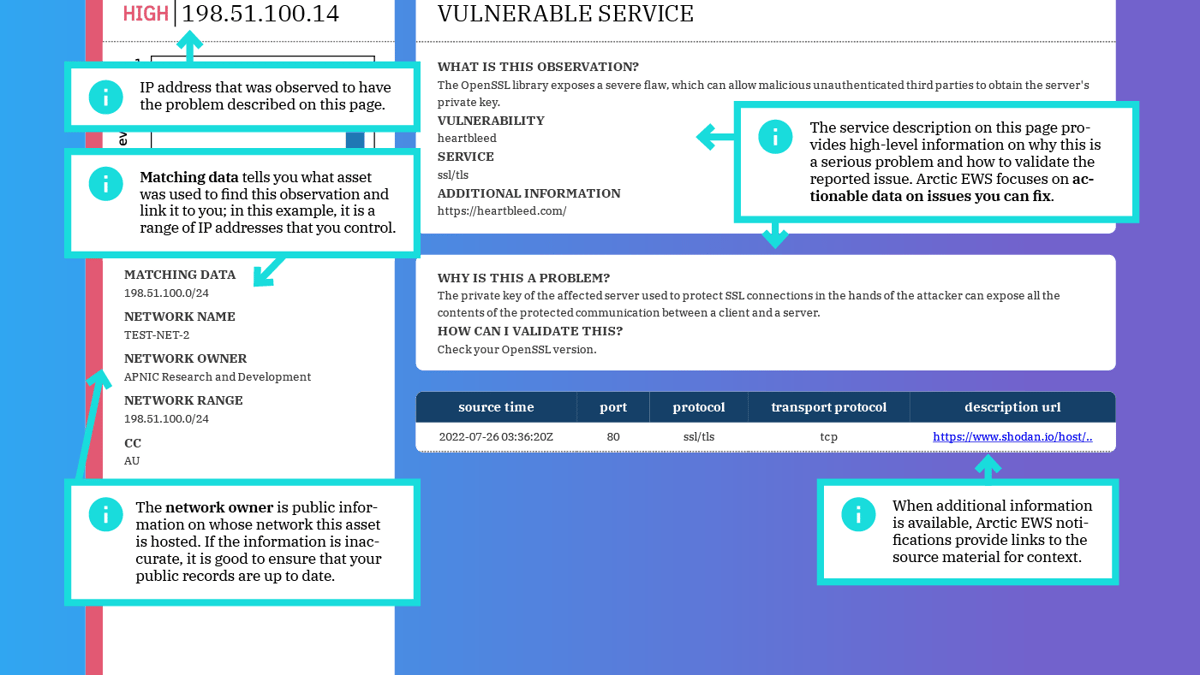
- Delivers fast and actionable threat intelligence
- Compliments your existing security measures
- Stops incidents before they happen
- Has been designed by experts with national cybersecurity experience
To start protecting your network in five minutes, hit the handy register button.
3 reasons to use Arctic EWS
Value for money
Today’s IT budgets are tight. As a start-up ourselves, we know what it feels like to work with limited resources. That’s why we’re determined to not only give you a premium, industry-leading service for a modest price, but to also make your first month free.
Always-on protection
Scheduled scans alone aren’t enough. In the time between scans, your network is vulnerable. With Arctic EWS, there is no “time between scans” – we watch over your network 24/7, 365 days a year.
Quick and
easy set-up
Our set-up form takes five minutes to complete. Seriously. Simply fill out the form by clicking on the button above and review your results. There’s no hardware or software to maintain – the only change to your day-to-day activities will be a new sense of complete security.
What our customers are saying
"Our notifications absolutely impacted our daily routine. We added them to our morning call. So, every day at 09:00, we go through all the help desk tickets and other alerts."
- Mark Herron, CISO at Case Western Reserve University
"You’ve helped us clearly identify unknown services running on our network that may be used for points of entry because of bad configurations, including unpatched systems, end of life systems, systems with default credentials or improper access controls."
- Harry H, CISO
