As cyber defenders, we need to recognize the simple fact that threat adversaries are highly organized and collaborative in nature, whether organically or not. Various threat actors who are specialists in their own field of expertise, banded together (whatever their motivation might be) have proven to be potent and highly successful. The proliferations of underground marketplaces further prove the point. But most of the messaging from security vendors is about equipping organizations to defend from their silos. They talk very little about the collaborative nature of the threat landscape.
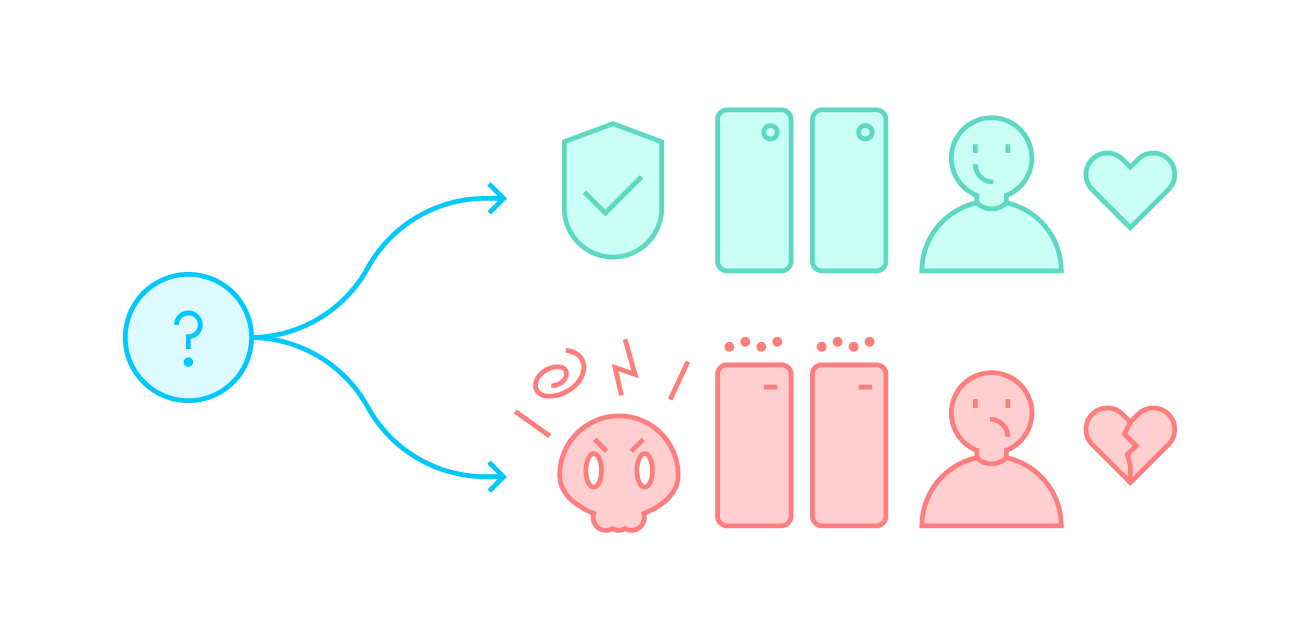
Let’s be candid when it comes to cybersecurity: it is never a core business for most of the organizations if they are neither a security vendor nor a services company. Thus, getting an IT budget and spending on security specifically is always challenging. Business owners or executives will always measure with these two yard sticks:
- Return on investment
- Business impact of implementing vs. not implementing
A simple answer is ‘relative’. Any security investments should be relative to the size and scale of the business of an organization. Cyber threat intelligence (CTI) is no different as well. Gone are the days where threat intelligence is offered as an add-on like a Happy Meal™. According to the latest SANS 2018 CTI survey, most respondents agreed CTI is becoming more useful overall, especially to security operations teams. This has led to an increased deployment rate of standalone CTI platforms.
Any organization starting its CTI program should realize that threat intelligence is a process. But this doesn’t necessarily mean it has to be manual or difficult in terms of cyber intelligence. Neither it is cost prohibiting if one knows the right sources where to digest from and how to do that. There are plenty of quality open source and private threat feeds available. For example, ShadowServer produces over 40 different types of feeds alone.
Recognizing but more importantly, owning, the collection of threat intelligence is critical. You should be empowered to dictate the collection effort, regardless of formats or methods. And through automation, to help you focus on the intelligence that matters most for your organization.
One of the biggest challenges is how to make sense of the indicators collected. Sure, there are tons of indicators of compromise out there, such as the ones provided by Brute Force Blocker by Daniel Gerzo or vulnerable Netis router services by ShadowServer. But a system that could automate every single indicator you collect and inform you about the details behind every IP address can make a real difference. The details include things like the country of origin of an IP address, its network operator, which critical infrastructure it may belong to, a geo-location of the affected machine, or even its organization owner. With contextual information you can get and therefore focus on the real intelligence which requires human touch.
No more alert fatigue, no more mundane tasks of searching or querying or reading large amounts of text or reports. Focus on actionable events on which you can take action, either as an analyst, a sysadmin or a network admin. The very same platform also allows your risk management team to conduct threat assessments and helps your organization posture and formulate security strategies and policies respectively. Justifying a security investment with the hard evidence and metrics is now much easier.